Shark Jack

What is Shark Jack ?
The Shark Jack is a portable network attack and automation tool for pentesters and systems administrators designed to enable social engineering engagements and opportunistic wired network auditing.
It features a familiar Hak5 payload architecture, flip-of-the-switch operation and multi-color LED for instant feedback.
The Shark Jack is meant to be deployed against a target network for brief reconnaissance, exfiltration and IT automation tasks. With a fully charged battery, the Shark Jack will operate for about 10-15 minutes.
Out-of-the-box, a pre-installed default payload executes an nmap scan of the connected target network when the switch is in the attack mode. This default payload saves the scan results to a loot directory on the device.
Payload
I write several payload who are available on my github https://github.com/julesbozouklian/shark_jack_payload
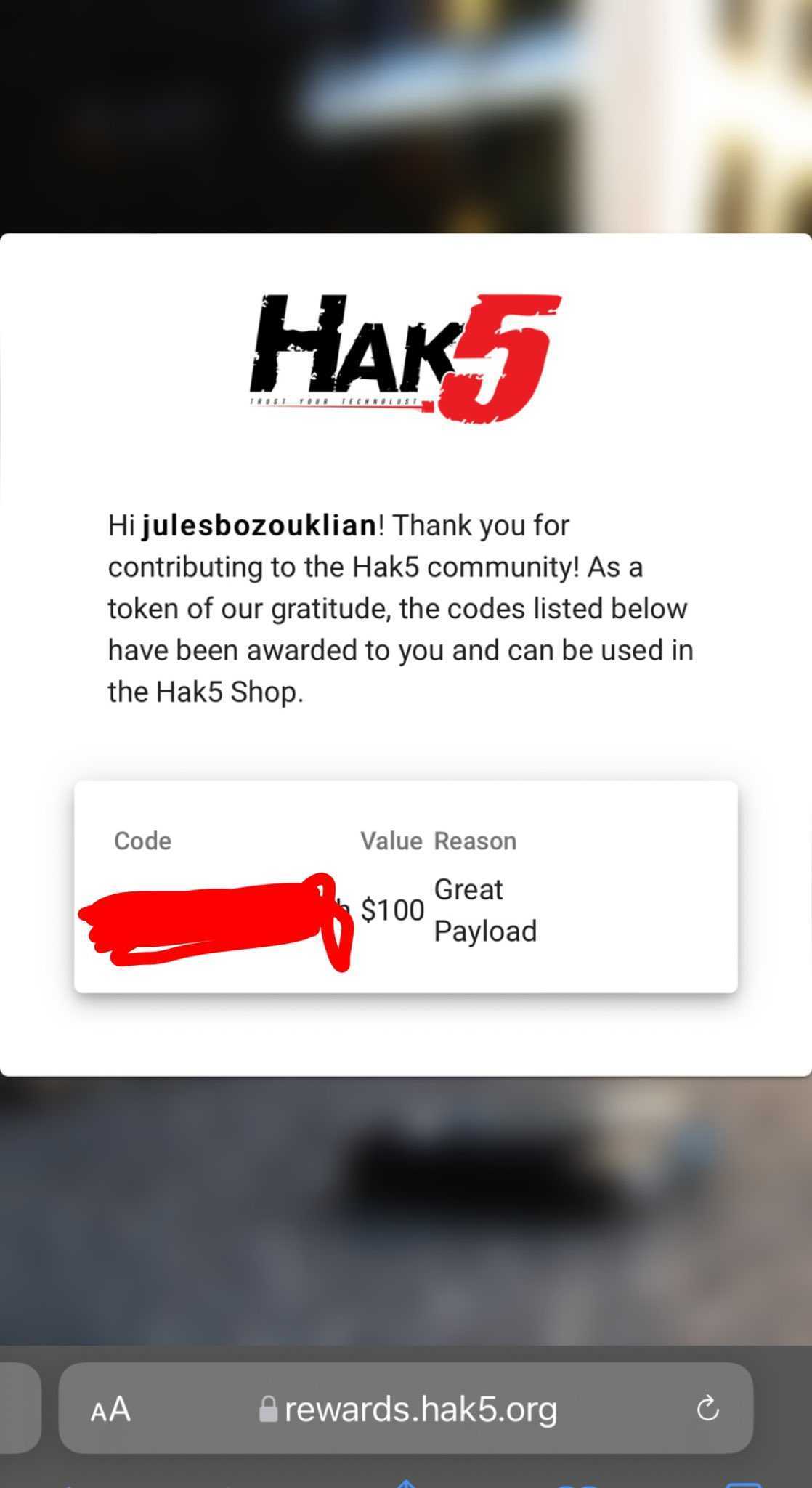
Thanks to hak5 who selected my payload to exfiltrate data with microsoft teams and gift me $100 voucher
https://shop.hak5.org/blogs/payloads/ms-teams-exfiltration
